October 19, 2021
Privacy Tip of the Week: Password Protect Your Smart Devices
Posted by Rhiannon
The world we live in today is a “smart” one. Smart devices number in the billions and range from smartphones and tablets to home thermostats and digital assistants. In general, they make life easier but there’s often a trade-off as they may collect your personal data. Some devices, like smartphones, keep that information within their own memory storage. Other devices, which don’t have storage built in, send the data they collect to servers owned by the device manufacturer. Unfortunately, having your information stored anywhere opens you up to the risk of data theft. On the bright side, you can protect yourself if you password protect your smart devices. Here’s what you should know:
- The two types of password protection
- Your personal information
- Why should you password protect your smart devices?
- Password tips
- Other ways of protecting your devices
The Two Types of Password Protection
For the purposes of this article, we have divided smart devices into two different categories. The first category is ‘directly-accessible devices.’ These include smartphones and tablets, where the information collected and stored by them is directly accessible through the device itself. The second category is ‘remotely-accessible devices.’ This category includes things like smart speakers and thermostats, where the information collected by them cannot be accessed directly through the device (typically because they don’t have screens with which to navigate them). Instead, the devices are accessed remotely, through the use of an app.
While you must protect each type of device, the mechanism for doing so is slightly different.
Directly-Accessible Device Passwords
It is absolutely imperative that you password protect your directly-accessible devices, such as smartphones and tablets. However, a poll by security company McAfee found that more than 30% of people do not password protect them. Unfortunately, this is one of the single greatest threats to data privacy, due to the fact that these devices are the access point for nearly all of our personal information. Our mobile devices contain some of the most basic data about us, like our contact information and addresses. However, they also grant access to other services, like social media, email, and banking, and often don’t require the user to sign in every time. In addition, they typically house the apps used to access our remotely-accessible devices. An unlocked smartphone just lying around can surrender access to every element of our lives to anyone who just happens to walk by and take it.
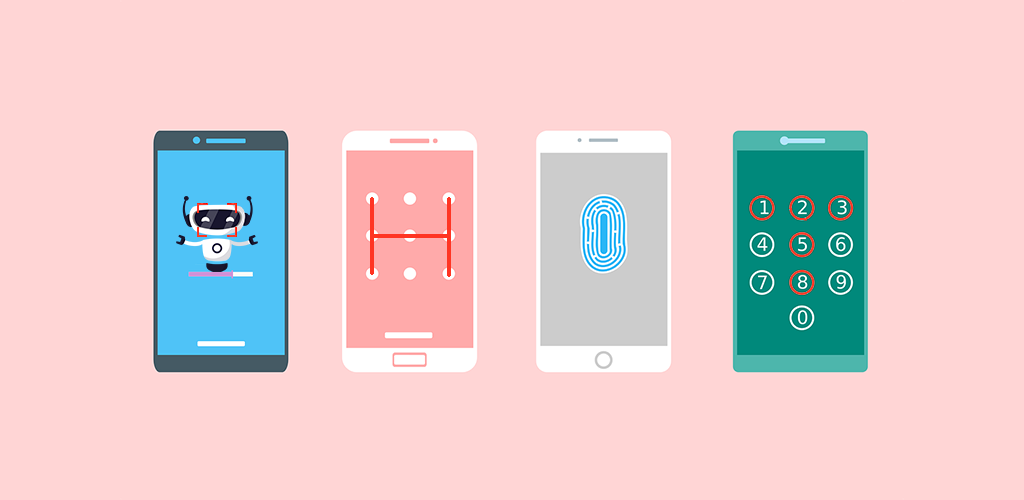
Fortunately, mobile devices allow you to add a password that must be used every time you access the device. While most online accounts only offer character-based passwords, many mobile devices give users a choice of password type. Users may be able to still use character-based passwords, or may choose a PIN, pattern, or even biometric security (which relies on scanning your fingerprint or face).
By password protecting your mobile devices, you also add a layer of security to most of your remotely-accessible devices.
Remotely Accessible Device Passwords
While directly-accessible device passwords help protect your remotely-accessible devices (if they contain access to the apps for each remote smart device), you should still password protect each remote device you have, such as smart speakers/digital assistants, thermostats, lights, locks, and more. These devices are closely linked to your personal life and, if access to them falls into the wrong hands, it could be used to wreak havoc on your life.
Fortunately, most of the apps that allow you to control your devices require that you password protect them. While these apps most typically offer character-based passwords only, some may allow you to also use two-factor authentication, which we’ll discuss below.
Your Personal Information
The biggest risk you take when you don’t password protect your smart devices is that your personal information may be stolen. This might not seem like a huge danger to some. However, the data you risk is more important than many people realize.
If your directly-accessible mobile devices are stolen, the thief may:
- Steal your contact information. They can use it to make calls in your name, scam your contacts, or build a profile with which to steal your identity.
- Gain access to your other accounts. Most of us use our mobile devices to access our other accounts without having to sign into their respective apps. These accounts may include email, Facebook, banking, and more, all of which a criminal can use against you, or as you (which can get you into a world of trouble).
- Use your mobile payment services. If you use your smartphone’s mobile wallet to pay for goods and services, anyone who steals your unprotected device can access this wallet too.
- Collect other information about you and your personal life. Your phone’s GPS might give away your home address, and your camera roll can tell them a lot about your personal life. These are far from the only examples of ways a thief can steal your information directly from your smart devices.
If a cybercriminal gains access to your remotely-accessible smart devices, they may be able to:
- Unlock your doors. If you use a smart lock on your front door, a criminal who gains access to the account that controls it can stroll right into your house and steal all of your physical belongings.
- Listen to your conversations. Conversations you have with your smart speakers are often transcribed into the app that controls them. A person who gains access to this app can also snoop on your conversations.
- Spend your money. If your smart speaker is able to buy products from ecommerce stores like Amazon, theoretically, so could a thief.
- Turn your thermostat up or down. This can result in obscenely high bills or, in some cases, home damage (for example, if a criminal turns your thermostat off in the winter months, pipes could burst and cause water damage).
- Access your cameras. If you use smart-cameras to monitor your home, a person with access to the viewing app can also monitor your home…with you in it.
- Control your lights. Remotely-controlled smart bulbs can also be controlled by someone who gains unauthorized app access. While this might seem like a silly prank at worst, if you use the same password for all of your smart device apps, someone getting access to your light setup might be a sign that they have access to other smart devices in your home.
Why Should You Password Protect Your Smart Devices?
By now, you know that you should password protect your smart devices to prevent your most sensitive data from falling into the wrong hands. However, knowledge of this risk often doesn’t spur people to action, because it seems abstract and far away. Many people know there is a risk, but don’t do anything about it simply because they don’t think the threat could ever impact them. If you fall into this category of people, here are some real-world examples of why password protecting your smart devices should be on the top of your to-do list:
Thieves Can Easily Steal Your Phone
If you’re like most people, you probably bring your smartphone everywhere you go. Shopping at the mall? Check. Out to dinner? Check. On vacation? Check. Unfortunately, by taking your device everywhere, you could lose it or have it stolen anywhere. All it takes is a moment of inattentiveness or a trip to the washroom for any thief to casually slip your phone into their pocket. If you don’t password protect your device, this thief now has access to your contacts, photos, apps, banking information, and more. If you’re lucky, they’ll factory reset the phone (thus deleting your information) and use it or sell it. But if you’re unlucky, they’ll use your data to wreak havoc on your life.
Nosiness is Everywhere
Faceless strangers with a penchant for thievery are not the only risk to your devices. In fact, the nosiness of the people you know might pose a greater threat to your unlocked devices. A co-worker who snoops when you walk away from your desk might find out you’re searching for a new job from a private email and rat you out to your higher ups, making things awkward. A jealous partner might search through your conversations with others, hoping to start a fight or exert control over you. Even your kids can find the Amazon app and order hundreds of dollars worth of toys without your knowledge.
Your Unprotected Devices Can be Searched
Hopefully, law enforcement agencies never have reason to suspect you of a crime. But, if this should happen to you, it’s possible that the agency you’re dealing with may be able to search your phone, tablet, or other smart devices to look for evidence that ties you to the crime they believe you committed. However, you can help prevent or at least delay this by always protecting your devices with a password. This article has more information about what law enforcement can and cannot do with your password protected data.
Smart Device Password Tips
Whether you’re securing a directly-accessible device, or the apps needed to access remote smart devices, there are some best practices you should follow when creating a strong password.
In general, best practices include:
- Using a long password
- Making the password unique
- Using something impersonal
- Getting artsy
Using a Long Password
Simply put, the longer your password, the harder it is for device access to be stolen. Some devices only allow you to use a four-digit PIN but, where possible, you should aim for something longer. Most recommendations suggest using between 12 and 16 characters, but the longer the password, the better.
Making the Password Unique
In a recent survey, the most vulnerable passwords were also the most widely used. They included “123456,” “111111,” “qwerty,” “abc123,” and the old classic, “password.” While those passwords might be easy to remember, they’re also easy to guess and put your information at risk. Instead, use something with a blend of letters, numbers, and symbols, as well as capitalized and lower-case letters.
Using Something Impersonal
Because the best passwords are long and unique, it’s usually easier to create one that means something to you, so you remember it easily. However, passwords that are too personal also put you at risk. Many people incorporate elements of their name or the name of a loved one, birthday, phone number, or even social security number. If this information can be found in places like your social media accounts, for example, then anyone who can see your account can also use your personal information to guess your password.
The best passwords don’t contain personally identifiable information, or dictionary words (ie. a word you could look up in the dictionary right now). However, if you’re afraid that you’ll forget a password that’s little more than a jumble of letters and numbers, there are tricks you can use to remember them. For example, you can make a mnemonic password from a memorable phrase. The phrase “My favourite movie is The Princess Bride (1987),” can be turned into the password “MfmiTPB(1987).” You can also use a password manager, like LastPass, to keep track of your passwords for you.
Getting Artsy
Some devices allow you to trace a pattern as your device password. It’s a secure, easy to remember (and somewhat more fun) way of securing your phone. However, a study from the Norwegian University of Science and Technology found that most people use a predictable pattern. The study learned that the majority of users start their pattern in the corner of the screen, and draw out a letter (most often their first initial). Using something different than that will help ensure more security for your device.
Other Ways of Protecting Your Devices
Password protection is an important first step towards protecting your smart devices. However, there are other tips you can use to increase your security even more.
- Use two-factor authentication
- Turn off screen notifications
- Download a VPN
- Sign out
Use Two-Factor Authentication
Normally when you sign into your account, you type your username, you type your password, you hit enter, and you’re in. Unfortunately, if your password is weak or compromised, anyone who gets access to it can also sign into your account without your knowledge. However, with two-factor authentication, every time you sign in, you will also have to input a one-time code sent directly to a device of your choice. Even if someone else has access to your password, without your device, they won’t be able to access your account.
Turn Off Screen Notifications
One further step you can take is to turn off your lock-screen notifications. Even if your device is password protected, losing it can still be harmful if a thief can see your notifications. They might be able to learn enough information about you and your life to do some serious digital damage.
Download a VPN
A VPN, or virtual private network, is a digital tool that enhances user privacy online. It does this first by encrypting your activity. In this way, no one but you and the websites you visit can see what you’re doing. Secondly, a VPN temporarily changes your IP address. This prevents snoops from tracing your activity back to you, making you virtually anonymous. While a VPN can protect you every time you browse, it’s especially effective when you’re using public wi-fi. For example, if you sign into your device accounts on public wi-fi, anyone else on that network can theoretically see your activity and record your password. However, with a VPN, your activity becomes encrypted and hidden from prying eyes.
Sign Out
We know; it’s more convenient to stay signed in to your accounts than it is to input your credentials every time. However, it’s far safer for you to sign out. This way, if someone gets ahold of your smartphone, for example, they won’t also get access to the rest of your accounts as well.
To help you craft the strongest and most memorable password, check out our blog post on just that. This will help you password protect your smart devices as effectively as possible.
At HotBot, your privacy matters; that’s why everything we do puts your privacy and security first.
Posted by Rhiannon
More Blog Posts
February 14, 2023
How the Investigatory Powers Act Impacts Citizen Privacy
In 2016, the United Kingdom passed the Investigatory Powers Act or IP Act, into law. This act empowered the government and related agencies to access and collect citizen data, without consent. Critics immediately slammed the new law. The media dubbed it the “Snoopers’ Charter.” Meanwhile, Edward Snowden described the act as “the most extreme surveillance […] Read moreFebruary 14, 2023
How to Easily Unblock Wikipedia with HotBot VPN
Wikipedia puts a wealth of information at your fingertips. Everything from the biography of Alexander Graham Bell to the basics of quantum computing can be instantly opened by curious browsers. But what happens when you can’t access that information? Whether a business network blocks it or a particular country censors it, don’t let that slow […] Read moreFebruary 14, 2023

