October 12, 2022
The Basics of Email Phishing
Posted by Rhiannon

The concept of email – short for “internet mail” – predates the internet by decades. In 1965, computers at MIT were loaded with a program called MAILBOX, which allowed a user to leave a message for another user on the same computer, which they would see when they logged in. This system was limited and only effective for users of the same computer. The creation of the internet made email far more functional, and that function has only increased. Today, roughly 4.6 billion people around the world use email. Unfortunately, that means 4.6 billion people can be targeted in elaborate phishing attempts. Let’s take a look at what email phishing is, how it might be achieved, the ways you might be able to recognize it, and how you can protect yourself against it:
- What is phishing?
- The types of email phishing
- How do you recognize phishing?
- The ways to protect yourself
What is Phishing?
Phishing is a type of cyberattack where the attacker tricks their victims into giving up personal information like login credentials or credit card numbers. It can happen through a few different channels, including email (the topic of this article), text and instant messaging, phone calls, and fraudulent websites. Phishing is one of the most effective cyberattacks out there because it uses a tactic called “social engineering.” Social engineering uses psychology to essentially weaponize what people trust, and what people fear.
For example, if an attacker wants to learn your online banking credentials, they’ll use a combination of sophisticated web design and social engineering. The web design element allows them to create an email and website that looks like it belongs to your bank. With social engineering, a clickbait subject line like, “Your account has been breached. Change your password now,” is typically enough to alarm the recipient into immediately clicking whatever link is in the email, thinking it will take them to their bank’s login webpage. An experienced attacker will ensure that the resulting webpage will also look like it belongs to the bank. As soon as the victim types their login credentials into the right places, the attacker will use that information to access the victim’s real bank account and whatever money they might have.
Phishing attacks typically aim to steal money directly from the victim. However, they may also target the victim with the aim of stealing their identity or sensitive information that can be used for blackmail. In addition, some phishing attacks aim to trick the victim into downloading malware onto their devices.
The Types of Email Phishing
Although the aim of phishing is to steal money or information from the victim, attackers can go about phishing in a few different ways. Some of the types of email phishing include:
Mass-email
With this method, the attacker will send a fake email to thousands of recipients and hope that a small portion of them fall for the scam. For example, the attacker might create an email that looks like it’s from Citigroup bank, warning users to change their passwords. Only a fraction of recipients will even have accounts with Citibank, and a portion of those will recognize the attempt as an attack. However, another portion will fall for it and accidentally give up their banking credentials.
Spear phishing
This method is more effective but far more time consuming. With spear phishing, the attacker will specifically target and research their victims (to an extent). For example, the attacker might choose a target, like the accounting manager, from a business’ employee directory. Knowing that the target is the accounting manager allows them to craft an industry-specific email with a link to a downloadable file that contains a malicious program. If the attack is done well, the victim might click the link without even considering that it might be spam.
Whaling
Similar to spear phishing, the attacker in this case specifically targets the highest up or most important member of an organization, like the CEO or CFO. These emails commonly claim that a company is facing legal action and directs the recipient to follow a link to learn more. The link might then take them to a webpage asking for user information, or it might initiate the download of a malicious file/software.
Sextortion
This method focuses on blackmailing the victim, rather than trying to trick them out of their information. With sextortion, the attacker sends the victim an email claiming, for example, that they have a video of the victim watching adult content on their computer with their webcam on. The attacker will threaten to release the video if the victim doesn’t pay them (commonly in Bitcoin or another cryptocurrency).
How Do You Recognize Phishing?
Some phishing attempts are extremely sophisticated, and even the most trained eye might not recognize it. However, in most cases, there are some red flags that an email might not be what it appears. Common signs of phishing include:
Bad spelling and grammar
Official emails from real companies tend to be thoroughly proofread and free from spelling or grammar mistakes. If an email looks official but is riddled with errors, it might be a phishing attempt.
The greeting doesn’t fit the email
Often, cyberattacks come from people who are citizens of other countries, so they might not have a strong grasp on your primary language. As a result, some of the phrases they use might be strange in context. If an email allegedly from your bank starts with the greeting, “my love,” you should be suspicious.
Emails that demand urgent action
Most phishing attacks attempt to encourage the victim to panic and take immediate action. While real emails may do the same thing, by treating all urgent action requests as phishing, you can more carefully vet the source to ensure it’s from a sender you trust.
The email address isn’t what you expect
It’s a great idea to get into the practice of checking the sender’s address every time you open an email. If the email looks like it comes from Citigroup Bank but the sender’s address is “[email protected],” you can probably disregard the email in its entirety.
The email is too good to be true
If you receive an email claiming you’ve won a prize from a contest you didn’t enter, the odds are good that you’ve received a phishing email.
An attachment is included but shouldn’t be
If you receive an email with a file attachment that you wouldn’t expect to be there, don’t click the attachment unless you can verify that it is safe and authentic.
The Best Ways to Protect Yourself From Phishing
Learning to recognize phishing emails is the best way of protecting yourself from them. However, there are a few other tactics you can use:
Use a powerful VPN when you browse the web
In order to send you a fraudulent email, a cyberattacker first needs to know your email address. One of the ways they can do this is by stealing it from a poorly encrypted website. By using a VPN, you can add extra encryption to any website, thus helping to avoid the possibility of phishing altogether.
Never click an in-email link unless you’re 100 percent sure it’s safe
For example, if you get an email from a company requesting that you change your account password, don’t use the in-email link to navigate to that website. Instead, use your browser bar to navigate to it yourself and change your password that way. The same goes for promotional emails from companies proclaiming sales events; don’t visit their website via an email link. Type the URL into your search bar instead.
Always check the sender’s address
We mentioned this tactic above but it’s worth repeating. Every time you receive an email, check the sender’s address. This helps you ensure the email has come from a source you trust or can verify.
Use smart password practices
If you do end up falling for a phishing attempt, you can help to mitigate the damage by using password best practices. For example, if you reuse your passwords on multiple platforms, a cyberattack who gains access to one website can theoretically login to all of your accounts. This cannot happen if you don’t reuse passwords. A password manager can help you use strong, unique passwords for each website.
There are 4.6 billion people around the world who could fall victim to a phishing attack. You can ensure you won’t become one of them by understanding how phishing works, learning how to recognize an attack, and using best practices to avoid phishing.
Posted by Rhiannon
More Blog Posts
February 14, 2023
How the Investigatory Powers Act Impacts Citizen Privacy
In 2016, the United Kingdom passed the Investigatory Powers Act or IP Act, into law. This act empowered the government and related agencies to access and collect citizen data, without consent. Critics immediately slammed the new law. The media dubbed it the “Snoopers’ Charter.” Meanwhile, Edward Snowden described the act as “the most extreme surveillance […] Read moreFebruary 13, 2023
How to Bypass Censorship with the Best VPN Services: A Guide to Unrestricted Internet Access
Are you tired of facing internet censorship and restricted access to information? A Virtual Private Network (VPN) can help you bypass censorship and enjoy unrestricted internet access. In this guide, we'll explore how a VPN works to bypass censorship, the benefits of using a VPN, and what to consider when choosing the right VPN for you. Don't let censorship limit your online freedom, discover the power of a VPN today. Read more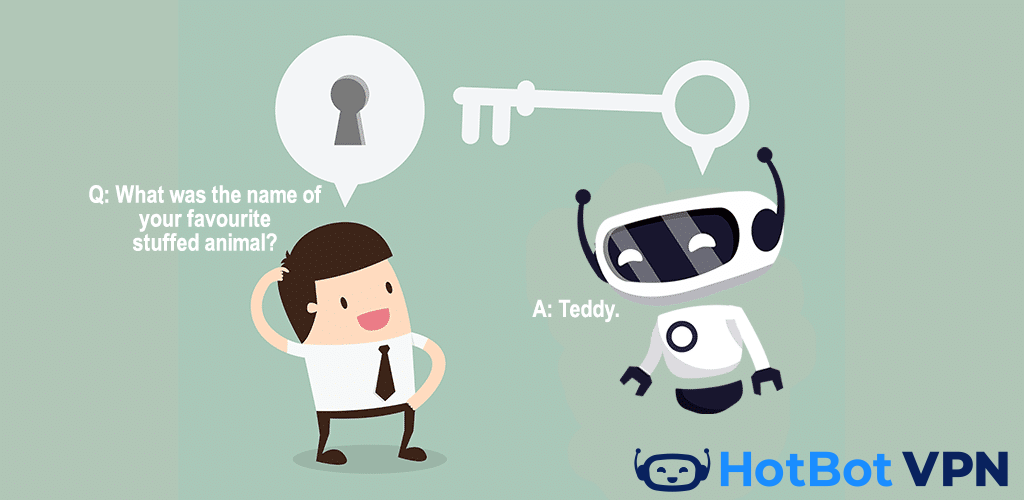
January 21, 2023

